Complete Cybersecurity
Every Layer. Every Threat.
One Las Vegas Team.
In 2026, cyberattacks hit your endpoints, firewall, cloud infrastructure, email, and employee identities simultaneously. Protecting just one layer leaves every other door open. Dzinex delivers unified, full-spectrum cybersecurity — monitored 24/7 by human analysts and AI — so no attack vector goes unguarded.
Built for Las Vegas organizations with 10 to 1,000+ employees. Endpoint, network, firewall, cloud, identity, and email — all under one managed security program.
Unprotected Endpoints & Servers | Exposed Cloud & Firewall | No 24/7 Security Monitoring |
$4.88 M
Average cost of a data breach in 2026
94%
Of cyberattacks start at the endpoint
72 hrs
GDPR / Nevada law breach notification window
< 1 min
Dzinex threat detection & isolation response
THE 2026 THREAT LANDSCAPE
Las Vegas Businesses Are Being Targeted
By 6 Evolving Cyber Threats Right Now.
Cybercriminals don't take days off. They attack Las Vegas hospitality,
healthcare, legal, financial services, and construction companies every
single day — often for months before anyone notices.
$1.54M AVG RANSOM PAID — 2026
Ransomware & AI-Powered Malware
Modern ransomware uses AI to evade legacy antivirus, encrypt your data in minutes, and simultaneously exfiltrate it for double extortion. Las Vegas businesses in hospitality, healthcare, and finance are prime targets.
$340% RISE IN AI-GENERATED PHISIHING — 2026
Spear Phishing & Business Email Compromise (BEC)
Attackers use generative AI to craft perfectly personalized emails that fool even trained employees. BEC alone cost U.S. businesses $2.9 billion in losses last year — and it starts with one inbox.
80% OF BREACHES INVOLVE STOLEN CREDENTIALS
Credential Theft & Identity Attacks
Weak passwords, password reuse, and MFA bypass attacks give attackers silent access to your systems for an average of 194 days before detection — without proper endpoint monitoring.
60% OF BREACHES EXPLOIT KNOWN UNPATCHED VULNERABILITIES
Unpatched Endpoints & Zero-Day Exploits
Every unpatched laptop, workstation, mobile device, and server is an open door. Zero-day exploits are sold on dark web markets and weaponized within hours of public disclosure.
60% OF BREACHES INVOLVE CLOUD ASSETS
Cloud Misconfiguration & SaaS Exposure
Misconfigured Microsoft 365, Google Workspace, and AWS environments expose sensitive data publicly without your knowledge. Your SaaS stack is a massive attack surface most businesses leave wide open.
45% OF ORGS SUFFERED SUPPLY CHAIN ATTACK IN 2025
Insider Threats & Supply Chain Attacks
Malicious insiders, compromised third-party vendors, and software supply chain attacks bypass perimeter defenses entirely. Your weakest link may not even be inside your building.
The MGM Resorts breach cost $100 million in one incident.
A social engineering attack that began with a 10-minute LinkedIn search and one phone call to their IT help desk.
No business in Las Vegas — regardless of size — is immune. The question is not if you'll be targeted.
It's whether you'll be protected when it happens.
Think your business is too small to get hacked? think again
Cybercriminals often target small businesses, viewing them as easy targets with fewer security resources. In this case, SIZE does not matter.
Here's why your business, even if small, is a potential target for cyberattacks:
Cybercriminals often target small businesses because they are perceived as having weaker, relaxed security measures. Its a great place to test and practice malicious code.
Phishing, where criminals trick employees into revealing sensitive information, is a still one of the most common, easy and affective attack vector for small businesses.
Your staff is only as good as the training and tools used to protect your internal organization.
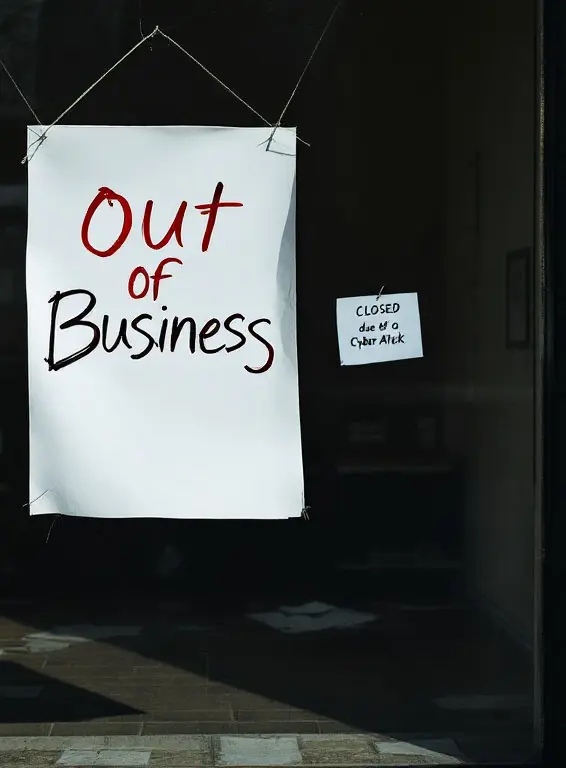
A significant percentage of small businesses that experience a cyberattack go out of business within six months. Cyberattacks can lead to business disruptions, financial losses, and damage to a company's reputation.
Protect Your Network Today – Every Minute Without Security Is Another Vulnerability Exposed. Don't let your next purchase be an Out of Business sign
Its protection, Its peace of mind
$200,000 in damages from a single cyber incident. At Dzinex, we've seen firsthand how proper security measures can be the difference between business as usual and business closure.
Isn't it time to protect what you've worked so hard to build
FULL - SPECTRUM CYBERSECURITY - LAS VEGAS & SURROUNDING AREAS
Every Layer of Your Business.
Monitored, Protected, Managed.
Dzinex delivers a Cynet-style unified cybersecurity platform — endpoint, network,
firewall, cloud, identity, and email security — all managed under one roof, one team,
one flat monthly fee.
- Pinpoint vulnerabilities
- Strengthen core defense
- identify network anomalies
- Shows lack in security practices
- simulates actual hacker attack
Continuously audit AWS, Azure, and Google Cloud environments for misconfigurations, exposed storage buckets, over-privileged roles, and compliance gaps. Most cloud breaches are caused by misconfiguration — we eliminate it.
Comprehensive monitoring of your SaaS environments — suspicious logins, OAuth app abuse, data exfiltration via email or Drive, admin privilege escalation, and anomalous file access all detected and blocked automatically.
Monitor Active Directory, Entra ID (Azure AD), and Okta for privilege escalation, pass-the-hash attacks, suspicious authentication, and unauthorized group membership changes — the most exploited attack vector in 2026.
Phishing-resistant MFA deployed across all applications, VPNs, and remote access. Zero Trust Network Access (ZTNA) principles applied — every user, every device verified before access is granted. Stops 99.9% of credential attacks.
Advanced email filtering that goes beyond spam — detecting BEC (Business Email Compromise), spear phishing, malicious attachments, impersonation attacks, and AI-generated social engineering before they reach any inbox.
Monthly interactive training modules, quarterly simulated phishing campaigns, and real-time in-the-moment coaching. Transform your workforce from your biggest vulnerability into your first line of defense.
HIPAA, PCI-DSS, SOC 2, NIST CSF, and Nevada NRS 603A compliance programs. Full SIEM log management and evidence collection. We prepare every document your auditors and cyber insurer demand — before they ask.
- Pinpoint vulnerabilities
- Strengthen core defense
- identify network anomalies
- Shows lack in security practices
- simulates actual hacker attack
One unified AI-powered platform that ingests and correlates security data across endpoints, network, cloud, identity, and email simultaneously — eliminating blind spots and alert fatigue. See every attack, across every layer, in a single console.
Your dedicated security operations team monitors, investigates, and responds to every threat around the clock. Human analysts backed by AI — no alert goes unreviewed, no incident goes unaddressed.
AI behavioral agents deployed on every laptop, desktop, and server. Detects ransomware, fileless malware, and zero-days in real time — isolating compromised devices in under 60 seconds before lateral movement occurs.
Continuous scanning of every endpoint and application for known vulnerabilities. Critical patches are automatically deployed during off-hours — no more forgotten updates that become breach entry points.
We manage, monitor, and optimize your firewall policies and rules — Fortinet, Palo Alto, Cisco, SonicWall, and more. Deep packet inspection, intrusion prevention (IPS), and application-layer filtering configured to your business needs.
24/7 monitoring of all inbound and outbound network traffic. Intrusion detection and prevention systems identify lateral movement, command-and-control beaconing, and data exfiltration attempts in real time.
Block malicious domains, phishing sites, and botnet infrastructure before packets reach your network. Enforced on every device — office, remote worker, and mobile — with category-based web policy controls.

Quarterly Penetration Testing.
The Dzinex Pen Test is a real-life demonstration of how hackers could get onto your business network, what they could steal or lock down, an easy checkup on user behavior and how IT has been managing things so far —a good test that they’re actually doing their jobs. Our test shows you how easy it is for hackers to get your information and makes sure your adhering to good cyber hygiene.
REAL RESULTS. REAL BUSINESS.
Las Vegas Companies that Didn't Get Breached.
COMMON QUESTIONS
Answers Before you Make The Call.
Traditional antivirus uses signature-based detection — it only catches threats it has already seen. Modern ransomware, fileless malware, and AI-generated attacks are specifically designed to evade antivirus entirely. EDR uses behavioral AI to detect anomalous activity in real time, even for brand-new zero-day threats. Without a SOC, those detections go unreviewed for hours or days. The combination of EDR + 24/7 SOC is the current minimum standard for meaningful endpoint protection.
Our EDR agent installs silently in the background — most employees never notice it. Baseline security configuration takes 5–7 business days. Full monitoring begins within 14 days of signing. There is zero downtime and zero disruption to productivity. We schedule all configuration changes during low-traffic windows.
Our SOC analysts receive the alert in real time. Depending on severity, they will: isolate the affected endpoint from your network, begin remote forensic investigation, notify your designated IT contact, and initiate remediation. For confirmed ransomware or active breaches, our incident response team engages immediately. This is all included — no extra incident response fees.
Yes. We have deep experience with HIPAA (healthcare), PCI-DSS (hospitality and payment processing), SOC 2 (SaaS and professional services), and Nevada's own NRS 603A data breach notification law. Our compliance program prepares you for audits, documents your security controls, and generates the evidence packages your auditors and insurers require.
Absolutely. Dzinex cybersecurity is designed to layer on top of existing IT support providers. We handle security exclusively — detection, response, patching, and compliance. Your MSP handles helpdesk and infrastructure. The two functions are complementary, not competitive. We work with your IT team daily.
If a threat reaches your environment and we fail to detect and respond within our contractual SLA, your next month of service is free. For qualifying incidents where our response met SLA but the breach still resulted in damage, we provide forensic investigation, documentation for cyber insurance claims, and remediation — all at no additional charge.
FREE SECURITY RISK ASSESSMENT
Find Out If Your
Business
Is Already
Compromised.
Our free 60-minute cybersecurity risk assessment scans your external attack surface, checks your endpoints, and reviews your current security tools. Most Las Vegas businesses are shocked by what we find — and relieved we found it first.
External attack surface scan (no agent required)
Dark web credential breach check
Current endpoint protection gap analysis
Top 5 vulnerabilities identified & prioritized
Written findings report delivered in 24 hours
Zero obligation — pure value, zero sales pressure
Response within 1 business hour
(702) 485 - 4020
Mon-Fri 8am-6pm PST - Emergency Line 24/7
3200 Polaris Avenue - #8 Las Vegas, NV 89102
Book Your Free Security Assessment
60 minutes. Zero obligation. Written report included.